We recently updated some security procedures including making running the OS firewall mandatory. The software was tested on Windows 10 and exceptions created in the GPOs for everything we found after installing ALL our software on several computers over several days.
But I made an oversight when testing the macOS software leaving out several categories of programs. Therefore the firewall was enabled in macOS and users almost immediately started receiving pop-ups to allow or deny known software.
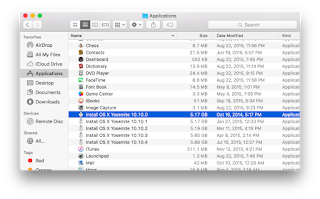
I configured the firewall using a profile created in Apple's Profile Manager that was edited down to only the required items for the task at hand. I was dismayed upon returning to Profile Manager the next day to discover that there was no way (at least that I could see) to add unlisted applications to the list provided in the browser. Of course, none of the items below appeared in the list despite being installed onto the mini.
After some quick Googling I turned to twitter and slack.
Hey @cedge318 is the procedure at the end of your post the only way to allow an app through the firewall that isn't showing up in Profile Manager's list?https://t.co/T2C283T2np pic.twitter.com/fH2436YrTJ— Ryan (@rmanly) April 19, 2018
@isaac responded in the macadmins Slack that adding exceptions was really quite simple
 |
10.12 does not have man page for socketfilterfw but 10.13 does!
|
Here are the items that needed to exceptions to prevent pop-ups.
- useragent = this is LightSpeed's binary that lives at /usr/local/bin.
- SMART Response = a piece of this here /Applications/SMART\ Technologies/Response\ Desktop\ Menu.app/Contents/Resources/
ResponseSoftwareService.app - TI CX CAS Teacher Software = this was in the firewall list on my buildbox so I either allowed it at some point or was playing around with the rules and forgot. Either way I'll just add it now. /Applications/TI-Nspire\ CX\ CAS\ Teacher\ Software.App
The firewall configuration profile was fine, it did exactly what I needed it to do and Munki won't install a profile again if it is exactly the same as an existing profile. So instead of changing the profile arbitrarily I am resolving this in two ways.
Solution 1
I've added a postinstall_script to the profile's installation instructions in munki and bumped the version to 0.2. This will take care of any NEW installations of the profile. So if any of the software exists on the system when the firewall profile is installed then the exceptions will be created.
Solution 2
I also created an update_for item for each of the affected apps in munki. These are simply postinstall scripts in pseudo payload free packages. This will not only add the exception rule to any existing installation of TI-Nspire, LightSpeed User Agent, or SMART Notebook/Response, it will also ensure that if these programs are installed in the future that the known exceptions will be applied. These are marked as unattended_install so munki will do them in background runs without user intervention.
socketfilterfw will also not error when a duplicate app is added so there is no problem if solution 2 is triggered after solution 1 is already applied.
In fact it doesn't appear to return proper error codes at all
>sad_trombone.mp3